Practical Layers of Business Security
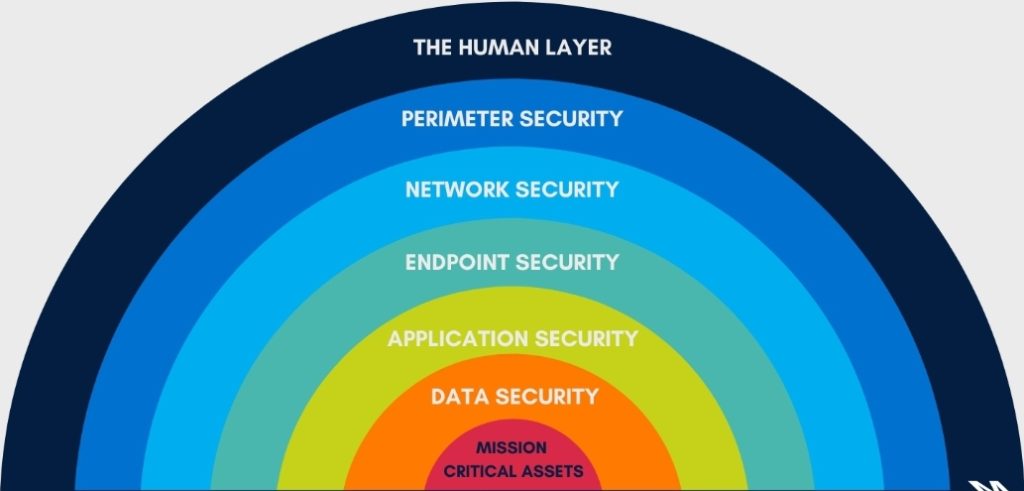
Most business owners don’t have time to deal with the nuance’s of cyber security. Seen below is the typical depiction of how security is managed in businesses today.
There’s an easier way of looking at this.
Sure there’s lots that goes into a fully secured business but it doesn’t need to be hard and its nearly free for small or one man operations. Here’s our steps in securing the digital assets of our customers:
Time needed: 2 hours.
Secure your businesses computers, mobile devices and servers. We suggest allotting 2 hours for this stage, but it can often take much less time to launch.
- Sign up for Antivirus if you haven’t already!
Our recommendation is Webroot Antivirus
- Install Antivirus on ALL devices, and we mean all your businesses devices
The great thing about Webroot is you can manage all your devices from one console. You can easily download and install on both your computer and phone, just login to the console and download the application
- Once installed, you can refresh your console in Webroot to see the health and status of all your devices
It’s as easy as 1-2-3. Your now protected against some of the nastiest and most used malware, trojans and computer viruses out there!
Now comes the more tedious part of making your small business secure for you and your clients… And that’s passwords.
Our suggestion for managing your businesses passwords is to use a password manager. Either hosted in the cloud or hosted on a local machine, but for a first time user, we suggest using a cloud based solution like LastPass since it’s easy to setup and use across multiple devices, seamlessly.
- Create an account with a Password Management Tool
- The password manager will ask you to create a Master Password, this should be long and hard to guess. NOT “Password12345!” or anything that could be connected to your personal life (some hackers will use personal information about you to hack into accounts, like your dogs name or the street you live on)
- After you’ve created your account we suggest taking the initial tour of the application, to learn the basics on how it manages your passwords
- Add all your account passwords to the “Vault”
- Download the mobile app (for using on your phone)
- Add the browser extension to your favorite browser (Chrome, Firefox, Safari, Explorer)
- Use the password manager to update / generate more secure passwords for your existing accounts
- Done
Our final suggestion for peace of mind is to use a backup tool to backup all your businesses critical data. For this you can use a variety of options, purely based on your preference and needs. We’ve listed some options below on how we backup our customers data. What this protects against is a worst case scenario, lets say a hacker gets access to one of your passwords or devices and they steal your data, holding it for a ransom payment. We’ll in this worst case scenario, you don’t have to pay, you’re not at the whims of a hacker, YOU have a backup! All you have to do is clean up the hack (change passwords and remove malware), then download your backup and you’re back in business.
- Google Drive (backup & sync
- 15 gigabytes free and it has a history tool which lets you pick the version of the documents you’d like to recover
- Upgraded storage is affordable
- Dropbox
- Good alternative to Google Drive
- Amazon S3
- Gives you more control over how your data is backed up, can add redundancies in the event of a corrupt or lost backup.
- Pay for what you need and not a penny more.
- Window Backup (requires either a local server or local drive to backup to)
- Less reliable but can definitely get the job done if you have the storage capacity.
That’s it, if you follow the above precautions you’ll be much more secure than before and at the lowest cost possible which is necessary for startups and small businesses alike. If you’d like help with the above for your business, give us a call, we’d love to be of assistance!
